Foundations Of Cybersecurity By Techknowsurge
Posted on 11 Aug 08:19 | by BaDshaH | 2 views

Published 8/2024
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Size: 15.55 GB | Duration: 9h 1m
Upsurge Your Cryptography Skills
What you'll learn
Define the definition and scope of the term cybersecurity
Explain key concepts associated with cybersecurity
Explain common vulnerabilities, threats, and attacks
Explain methods of protecting a cybersecurity domain
Define risk and explain methods of managing risk
Explain key concepts of Identity and Access Management (IAM)
Determine good password habits and what enforcement policies you should create in an organization
Explain access control steps and models
Explain key concepts for keeping data confidential
Explain key cryptographic concepts
Explain key concepts for keeping data integrity
Explain Public Key Infrastructure (PKI) concepts and processes
Describe mechanisms that help maintain high availability
Explain key concepts for incident response, disaster recovery, and backup solutions
Describes steps to secure enterprise equipment and networks
Requirements
No prior knowledge or experience needed, this is a beginners course
Description
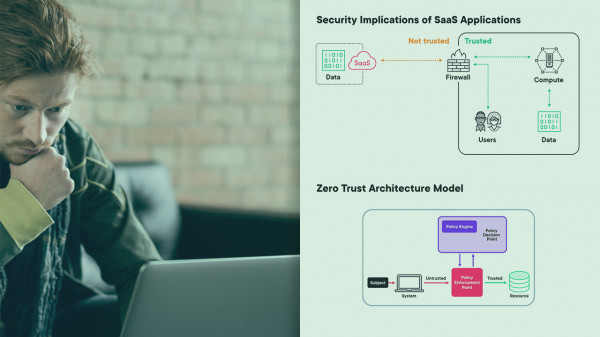
In this comprehensive course, participants will delve into the fundamental principles and practices of cybersecurity, equipping themselves with the knowledge and skills needed to defend digital systems and data against cyber threats. Through a structured curriculum, participants will explore the core concepts of cybersecurity, including threat identification, vulnerability assessment, and attack mitigation strategies. The course will cover essential topics such as risk management, access control mechanisms, encryption techniques, and identity and access management (IAM).Throughout the program, participants will gain a deep understanding of the cybersecurity landscape, learning to recognize and address potential risks that could compromise the confidentiality, integrity, and availability of information. They will explore real-world case studies and scenarios to apply theoretical knowledge to practical situations, developing critical thinking and problem-solving skills essential for effective cybersecurity practices.Key components of the course include:Understanding the nature of cyber threats, vulnerabilities, and attacks.Implementing risk management strategies to prioritize and mitigate potential risks.Utilizing access control mechanisms to control and monitor access to digital resources.Employing encryption techniques to protect sensitive data from unauthorized access or tampering.Managing digital identities and access privileges through identity and access management (IAM) solutions.By the end of this course, participants will emerge with a solid foundation in cybersecurity principles and best practices, prepared to contribute to the security posture of their organizations and navigate the evolving cybersecurity landscape with confidence.Explore the Mysteries of CybersecurityMaster Needed Cybersecurity Knowledge and Skills for IT Certification TestsLearn Foundational Knowledge to Accelerate Network and IT TrainingAccelerate Your IT CareerLearn it Right, Learn it Well, and Reap the RewardsSpending the time now to fully understand the core information of cybersecurity principles will help create a strong foundation to build off of.Who Should Take this Course:Those who are studying for an IT certification exam, to include A+, Network+, CCNA, Security+, CISSP, Server+, and ITF+Those who who are new to the IT field or trying to get into an IT careerAnyone who wants to have a better understanding of cybersecurity (even more advanced users can gain from certain modules in this course)System administrators, system engineer, network administrators, network engineer, system architects, network architects, help desk techniciansWhy take the course from me?Experience: I've been in the IT world since 2000, have a masters in computers, and over 20 industry standard certificationsKnow how to Teach: I was trained as an instructor by the USAF, have a bachelors in education, teaching since 1997, and well over 6,000 hours of classroom instruction time.I've been a hiring manager since 2010, I know what skill sets employers are looking for.TechKnowSurge's Unique ApproachYour instructor has training and years of experience as an educator, as a technician, and as a leader. The course implements the following features:Microstep lectures and segmented videos that meters learning into bite size chunks. It also makes it easy to go back and review concepts when needed.Staged-Based Educational Model where information is covered multiple times in increasing amounts of complexity. The approach helps reinforce learning and creates a knowledge and skill set less likely to fade with time.Extensive coverage of topics to make sure topics are explained fullyWell-organized content. A tremendous amount of effort has been placed on what order content should be delivered to maximize learning and minimizing confusion.A focus on pedagogy. A funny name, but your instructor has a deep understanding of educational theory and what drives learning.Module overviews explaining what to expect for each module and sets a mindset for why the information is important to learn.Video intros, overviews, and summaries to explain the intention of each video, reinforce learning, and prepare you for success.High quality and engaging videos that use graphics, great explanations, and analogies to explain complex topics in an easy to understand way.Real world application. Step beyond just the theory. Your instructor has real world experience and will share that with you throughout the course.Employer insight, know what employers are looking for. Your instructor runs IT Departments and hires individuals just like you.Content and OverviewThis course has6 Hours of contentWealth of informationAll designed to make you successful.Whether you are going for a certification, trying to break into a career in IT, or want to advance your career, IP subnetting is a fundamental part of the knowledge required for success. Get ready to level up your game. Join us now and let the subnetting fun begin!This well organized course will has the following modules:Course Introductions: Prepare yourself for efficiently and successfully completing the course. You'll get an overview of what the course is all about and what you should expect out of it.Defining Cybersecurity: This module introduces the fundamental concepts of cybersecurity, exploring its definition, scope, and importance in protecting digital assets from unauthorized access, breaches, and disruptions.Threats to Security: Participants will examine various types of cyber threats, including malware, phishing attacks, and denial-of-service (DoS) attacks, gaining insights into how these threats can compromise the security of systems and data.Protecting Against Threats: This module focuses on strategies and measures to mitigate cyber threats.Identity and Access Management: Participants will learn about the principles and practices of identity and access management (IAM), including authentication, authorization, and access control mechanisms, to manage digital identities and control access to resources effectively.Confidentiality: Exploring the concept of confidentiality, this module covers encryption techniques, data classification, and access controls to ensure that sensitive information remains protected from unauthorized disclosure.Cryptography: Participants will delve into the principles of cryptography, learning about encryption algorithms, key management, and types of ciphers, and how cryptographic techniques are used to secure data transmission and storage.Integrity: This module focuses on maintaining data integrity, covering methods such as digital signatures and database integrity mechanisms.Public Key Infrastructure (PKI): Participants will gain an understanding of PKI concepts and processes, including certificate issuance, revocation, and management, and how PKI facilitates secure communication through the use of digital certificates and public-private key pairs.Availability: Exploring the importance of availability in cybersecurity, this module covers strategies such as redundancy, fault tolerance, and disaster recovery to ensure that systems and data remain accessible and operational even in the face of disruptions or failures.Securing Your Network: Participants will learn about network security principles and best practices, including implementing secure configurations, segmenting networks, and monitoring network traffic to protect against unauthorized access and cyber threats.Wrap Up: Time to wrap up the course and provide any final thoughts.Instructor BioTechKnowSurge (Andrew Grimes) has been in the tech industry since 2000 and even longer as an Instructor. He started out as a Survival Instructor for the United States Air Force (USAF) in 1997. When he got out of the military, he started teaching computer classes. Wanting to advance his technical skills, he became a contractor working on a wide range of technologies while teaching technology college courses in the evening. Overtime, he became a hiring manager, director, and leaderHis background includes:Building a security program within 2 years to include becoming SOC 2 Type 2 compliantLeading and maximizing efficiency of IT, Security, and DevOps teamsManaging SaaS company infrastructure with millions of active usersManaging small, medium, and large IT InfrastructuresMigrating technologies to the cloudManaging multi-million dollar budgets and reducing overall budget spend year over yearUtilizing various project management techniques such as waterfall, scrum and Kanban to maximize efficiency and successBachelors in Workforce EducationMasters in Computer Resource and Information ManagementOver 6,000 hours of teaching experienceOver 20 industry standard certifications.Past student reviews:"Andrew is absolutely the best instructor I've had throughout the course of my education. He is extremely knowledgeable when it comes to all things network and IT-related. Because of the education he provided, I am now working in the network engineering field, and I could not have done it without his expert guidance." ~Michael B."Andrew was hands down my favorite instructor since enrolling" "He has great skills as an instructor, and I've learned a lot from his classes." ~Jeff S."As an instructor, he is thorough, articulate, patient and positive. He genuinely cares that his students fully comprehend the curriculum. I have a great deal of respect for Andrew. I can't recommend him highly enough." ~Dan H."I found Andrew to be one of the best Instructors" "He presents the information with real world applications, which helped to reinforce the concepts presented in the Cisco Certification track." "I am truely thankful to have had him as my teacher." ~Dan M."Andrew is very knowledgeable and brings his practical business experience with him. He expresses himself very well and treats everyone with respect. He explains very complicated concepts in a manner that is easy to understand." "It is without reservation that I would recommend Andrew as a business professional and/or teacher." ~Adam C."Andrew is an excellent instructor and more." "Andrew is the kind of teacher that you never forget." ~ William C."Andrew Grimes is a first rate instructor who genuinely cares about the success of his students. I was fortunate to have Andrew as my instructor." "I highly recommend Andrew as an instructor and IT professional." ~Paul C."Andrew is a great instructor who really cares whether his students grasp the concepts he teaches. He has a passion for teaching that many couldn't muster." ~Patrick R."He was a great teacher and I would gladly take a class under him again." ~Joshua R."...his style of teaching is accommodating for any level, that a student is starting off at, either beginning or advance in IT world." ~Paul W."He fosters a multidimensional environment of learning in which students of diverse abilities excel." ~Mark B"Andrew Grimes was a great Data Networks and Telecommunications Instructor." "I would highly recommend him to any who desires to further their education." ~ Tommy S.PrerequisitesNo prior knowledge needed
Overview
Section 1: Introduction
Lecture 1 Welcome
Lecture 2 Course Navigation
Lecture 3 Course Overview
Lecture 4 Syllabus
Section 2: Defining Cybersecurity
Lecture 5 Module Intro
Lecture 6 What is Cybersecurity
Lecture 7 The CIA Triad
Lecture 8 Cyber Incident Impact
Lecture 9 Key Cybersecurity Concepts
Lecture 10 Cybersecurity Cube
Section 3: Module intro
Lecture 11 Module intro
Lecture 12 Threat Agents
Lecture 13 Common Attack Vectors
Lecture 14 Common Vulnerabilities
Lecture 15 Common Equipment Vulnerabilities
Lecture 16 Common Software Vulnerabilities
Lecture 17 Race Conditions
Lecture 18 Social Engineering Techniques
Lecture 19 How Passwords are Hacked
Lecture 20 Malware
Lecture 21 Common Network Attacks
Section 4: protecting against threats
Lecture 22 Module Intro
Lecture 23 Protecting a Cybersecurity Domain
Lecture 24 What is a Cybersecurity Program
Lecture 25 Policies, Standards, Procedures, Guidelines, and Controls
Lecture 26 Types of Controls
Lecture 27 What is a Security Frameworks
Lecture 28 Risk Management
Lecture 29 Cybersecurity Lifecycles
Lecture 30 Basic Security Principles
Section 5: Identity and Access Management (IAM)
Lecture 31 Module Intro
Lecture 32 IAM
Lecture 33 Authentication, Authorization, Accounting (AAA)
Lecture 34 Password Habits
Lecture 35 Multi-Factor Authentication
Lecture 36 Password Enforcement
Lecture 37 Federation
Lecture 38 Access Control
Lecture 39 Access Control Models
Lecture 40 Physical Access Control
Section 6: Confidentiality
Lecture 41 Module Intro
Lecture 42 Confidentiality
Lecture 43 Data Lifecycle
Lecture 44 Encrypting Data
Lecture 45 Data Management
Lecture 46 Steganography
Lecture 47 Data Obfuscation
Section 7: Integrity
Lecture 48 Module Intro
Lecture 49 Integrity
Lecture 50 PKI and Digital Certificates
Lecture 51 Digital Signatures
Lecture 52 Database Integrity
Section 8: Availability
Lecture 53 Module Intro
Lecture 54 High Availability (HA)
Lecture 55 Measuring Availability, Five 9's, and SLAs
Lecture 56 Redundancy
Lecture 57 Replication
Lecture 58 Incident Response
Lecture 59 Disaster Recovery
Lecture 60 RPO and RTO
Lecture 61 Backups
Lecture 62 Backup Types
Lecture 63 Database Backups
Section 9: Securing Your Network
Lecture 64 Module Intro
Lecture 65 Physical Security
Lecture 66 Network Security
Lecture 67 Firewalls
Lecture 68 Remote access
Lecture 69 Equipment Hardening
Lecture 70 Host-Based Security
Section 10: Wrap Up
Lecture 71 Course Wrap Up
Those who are in or trying to get into a career that works with technologies that need to be networked,System administrators, system engineer, network administrators, network engineer, system architects, network architects, help desk technicians,Anyone who is studying for an IT certification exam, to include A+, Network+, and CCNA
Homepage
https://www.udemy.com/course/foundations-of-cybersecurity/
https://rapidgator.net/file/bcf1adb1c0a0c05fdbc484a2f781613d
https://rapidgator.net/file/909047a50dc2dfb6945a4582267a3726
https://rapidgator.net/file/a8e636ba64097becb90ecb92a5bce9e5
https://rapidgator.net/file/3b87e7c9e8673d3c11528608df1823ad
https://rapidgator.net/file/f67e58a2d977cf55523e34954c620c3c
https://rapidgator.net/file/2568e29d3ca73b7b47685c2e3f55e8c5
https://rapidgator.net/file/fd14873b05127a82b61b9d61d70b1beb
https://rapidgator.net/file/0a5a27deee6eeea611165a8d01cf97fc
https://rapidgator.net/file/3f44d7274666dad8595ed4a405c1bf2b
https://rapidgator.net/file/3219faeeb54497c4121ff9ba9174f18c
https://rapidgator.net/file/51672b310f9f9bcfd93e96efcc7da20f
https://rapidgator.net/file/a4aa5d0f4e6d05cefde4ff7460ed5f05
https://rapidgator.net/file/9d9f282e682b3572407bb033e6455ed3
https://rapidgator.net/file/42f928cdbbe39f6842228dc6806f8cf1
https://rapidgator.net/file/052f985e63e0e7572c54dd07d2362d34
https://rapidgator.net/file/d615ca9656e218edb9baa6d325e43ab2
https://rapidgator.net/file/fdc4390b00584a6ac48cd33b602828c1
https://ddownload.com/oard52etfgl9
https://ddownload.com/9ou6h5zn8nqe
https://ddownload.com/iefxediukd9m
https://ddownload.com/o4oc56d56xws
https://ddownload.com/mnv7elt222lt
https://ddownload.com/9w0f63ieagdj
https://ddownload.com/jmmf9cfheud2
https://ddownload.com/56ryukia5v3r
https://ddownload.com/1xbgg4dz4v3k
https://ddownload.com/dt1uj4zicz3c
https://ddownload.com/f01stsvnx97k
https://ddownload.com/vy0wduobvwep
https://ddownload.com/62poatf373rh
https://ddownload.com/uqm9802vafpu
https://ddownload.com/8m9pa1udi64e
https://ddownload.com/2rm93db1azq6
https://ddownload.com/hk1sha51n1zy
Related News
System Comment
Information
 Users of Visitor are not allowed to comment this publication.
Users of Visitor are not allowed to comment this publication.
Facebook Comment
Member Area
Top News